Top 20 passwords found in the Gawker dump
Interesting list of top 20 passwords in the Gawker dump. Hope you aren’t registered on any lifehacker/gawker sites!! http://ow.ly/3pUGl
.focus on your core business.
Increasingly, we are hearing in the news about cryptocurrencies like bitcoin, ethereum and dogecoin. A new facet of the conversation, …
… progress will only occur and accelerate if we facilitate the interaction between technologist and entrepreneur – and do it locally.

The deadline for meeting stage 2 standards of meaningful use of EHRs has been delayed until 2014 to encourage more physicians to participate.

An InfoWorld article summarizes the Verizon 2011 Data Breach Investigations Report(DBIR) and shows that – surprise! – the attackers are …
Interesting list of top 20 passwords in the Gawker dump. Hope you aren’t registered on any lifehacker/gawker sites!! http://ow.ly/3pUGl
TechRepublic’s Real-world server room nightmares. Check out these pics! I feel good for what we do for our clients… http://ow.ly/3pU4u
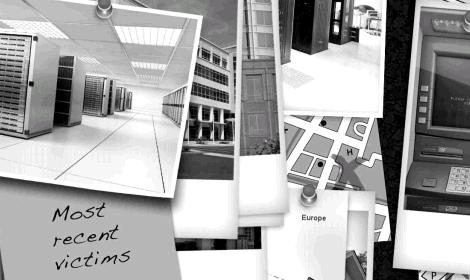
As computing has evolved, in the last 50 years, from facilitating only the core business processes to running every single process, the threats have multiplied to alarming levels. Information Security is no longer optional. It must be considered by any business, big or small. Defense-in-depth, a term once only used in military context, today describes how we approach securing your information and computing assets. A layering tactic, protection mechanisms, procedures and policies are put in place to increase the dependability of an IT system where multiple layers of defense prevent espionage and direct attacks against critical systems.
Using more than one of the following layers constitutes defense in depth: Physical security (e.g. doors and locks), Authentication and password security, Hashing passwords, Anti virus software, Firewalls (hardware or software), DMZ (demilitarized zones), IDS (intrusion detection systems), Packet filters, VPN (virtual private networks), Logging and auditing, Biometrics, Timed access control, Software/hardware not available to the public (but see also security through obscurity).
We provide solutions that secure your data and infrastructure using multiple layers of industry standard tools.
Are any of you making money from your blogs? http://ow.ly/3ozNS Interesting infographic says a lot of you are. http://ow.ly/3ozQk
The Economics of Cybercrime and the Law of Malware Probability. Great stats on underground malware economics. http://ow.ly/3ovhu
RT @itsecnews: Infosecurity (US): Senate bill would require minimum cybersecurity standards for internet … http://bit.ly/hV3P15
Latest Stuxnet variant evermore capable. Ecrypted bot communication makes it near impossible to analyse how it’s working. http://ow.ly/3nfhC
Passion is key to success in social media. So true! Who is passionate about your company. Empower them! http://ow.ly/3neeg
New malware encrypts your files and demands cash to decrypt them. Recommendation: encrypt your kids before they can! http://ow.ly/3m7r9
Love it! Touchless gesture-based interface devices for entertainment, healthcare. Swipe TV channels like ipod photos. http://ow.ly/3llhY