cyber assessments
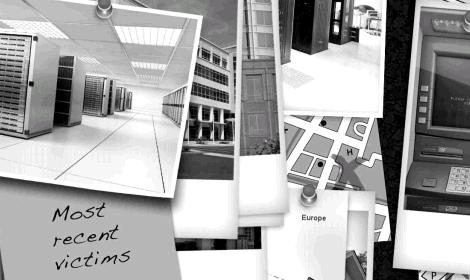
As computing has evolved in the last 50 years, from facilitating only the core business processes to running every single process, the threats have multiplied to alarming levels. Information Security is no longer optional. It must be considered by any business, big or small. Defense-in-depth, a term once only used in military context, today describes how we approach securing your information and computing assets. A layering tactic, protection mechanisms, procedures and policies are put in place to increase the dependability of an IT system where multiple layers of defense prevent espionage and direct attacks against critical systems.
Using more than one of the following layers constitutes defense in depth: Physical security (e.g. doors and locks), Authentication and password security, Hashing passwords, Anti virus software, Firewalls (hardware or software), DMZ (demilitarized zones), IDS (intrusion detection systems), Packet filters, VPN (virtual private networks), Logging and auditing, Biometrics, Timed access control, Software/hardware not available to the public (but see also security through obscurity).
We provide a framework based on the ISO/IEC 27001 Information Security Management System (ISMS) standard that organizes your policy and secures your data and infrastructure. We start by working with you to evaluate the fundamentals.
Risk Management
-Are we analyzing the InfoSec risks (confidentiality, integrity, availability) to the business?
– How are we measuring and prioritizing that risk?
Policy Management
– Do we have documented policies, procedures, and standards so that our workforce knows what’s expected of them?
Security Organization Management
– What’s our InfoSec team look like?
– Who does what?
Asset Management
– What the heck are we securing anyway?
– Can we track it?
HR Security Management
– Are we teaching our workforce how to securely use their computers?
– Do they know our policies?
– Do they know what social engineering is?
Physical Security Management
– What are we doing to physically protect our information systems?
Security Operations Management
– What does our InfoSec team do on a daily basis?
– Can we see what’s happening in our environment?
Access Management
– How are we controlling access to our systems?
– Are we operating under principle of least privilege?
– Is every ID in our access system appropriately restricted?
Information Security Systems Management
– Are our systems and apps configured with security in mind?
Security Incident Management
– In the event that something bad happens, does everyone know what to do?
Business Continuity Management
– In the event of a disaster (i.e., potential business-ending event), can we keep our doors open and our systems online?
– Do we have a documented plan?
Compliance Management
– What laws and regulations do we need to comply with?
– Are we complying?
The goal of Information Security is to secure and harden information systems to prevent the loss of:
– confidentiality, or the authorized, controlled disclosure of information.
– integrity, or the authorized modification or destruction of information, including verification of non-repudiation and authenticity.
– availability, the access to or use of information or an information system.
Although this Information Security Model, also known as the CIA triad, is theoretical and has it’s roots in military information assurance, IT security professionals use the framework as a starting point for discussion of Information Security for any business, regardless of size.
Get a Free Network Assessment! Learn if your network is properly configured for maximum speed, security and performance. We’ll look for hidden problems and other critical maintenance issues that can turn into extended downtime and expensive repair costs.
empowerT delivers a detailed Report Card that will show where you are vulnerable to security attacks, failures and compliance issues as well as provide recommendations on how to resolve these issues as quickly and inexpensively as possible.
Please call or text (469) 476-1972 today to learn more about a Free Network Assessment.

cybersecurity services
* network and application security assessments
* firewall and router installation and configuration
* vulnerability assessment and penetration testing
* federal compliance audits

managed services
* 24/7 network monitoring
* support help desk
* 90% of trouble resolved remotely
* vendor management

database services
* sql server, mysql
* reporting optimization
* sql mail scripting
* database upgrades

pixel . print . promo
* websites that work
* persuasive graphic design
* print from bizcards to booklets to billboards
* promotional products and apparel
* t-shirts